
Police CyberAlarm identifies and analyses suspicious data that is being sent to your systems by sources on the Internet. Your business or organisation receives thousands of these probes and attacks every day and will have network security devices that protect your systems from these requests; these devices are what Police CyberAlarm monitors.
When a data item (for example a file or email) is sent across the Internet it is broken down into thousands of tiny “packets” that can be transmitted. Once received, these tiny packets are then combined to rebuild the original item. Security devices can be divided into 2 categories: those that analyse the tiny packets; and, those that rebuild the original item and inspect it. In order to provide complete monitoring for suspicious data Police CyberAlarm can monitor systems in both categories, including the following systems.

Police CyberAlarm data is used to provide reports detailing the latest threats discovered, giving Member organisations the ability to update blacklists and other security measures to include new IP addresses and other relevant information to strengthen security. Monitoring for suspicious activity, providing assistance to you, the police, local business, and organisations within your industry.
A Firewall is an IT network device and is usually the first bastion of protection against internet threats, it is a very simple technology that blocks or allows data based on pre-determined rules defined by your system administrator. The rules are based on basic information in the “header” of each packet such as the source address, destination address and the port that the data is being sent via. By only using information in the header, firewalls are very fast and add almost no delay to the transmission.
A Firewall blocks the majority of unwanted and malicious requests from the internet so it is vital that Police CyberAlarm collect and analyse the logs from firewall devices. The logs provide information about what access was attempted, when and by what device. From this information we are not only able to detect whether an event could be suspicious, but also determine where it came from and how it tried to access your network.
Whilst firewalls block malicious traffic at the internet gateway based on rules defined by a network administrator, many organisations add a further security layer by monitoring their own networks for suspicious activity using Network Intrusion Detection Systems (IDS) and Intrusion Protection System (IPS) devices.
These systems inspect packet-level data which has been allowed by your organisation’s firewall device. The rules that NIDS/IPS use to determine if data is wanted or not are more complex than a firewall and include threat intelligence feeds of known bad source IP addresses as well as inspection of the whole packet, not just the header.
Collecting and analysing this data highlights traffic that may be allowed through the firewall but which is likely malicious, allowing member organisations to further improve their cyber security awareness and security posture. The logs sent to Police CyberAlarm contain the source and destination IP address of the traffic, and a summary of the access attempt.
Files sent through the internet can sometimes contain viruses that are designed to install malware on the recipient’s device. Most organisations will install Anti-Virus (AV) software on their desktop computers and laptops to protect their users, however this does not protect other devices such as switches and routers.
Network AV provides an additional layer of protection for users as well as protecting network devices and other systems that do not have AV software installed. These systems reconstitute the original data item being sent in order to scan it for malicious computer code.
Anti-virus logs contain information about the source of the email and the IP address of the intended recipient, as well as the message subject and attachment name but do not contain the body of any communication.
Anti-SPAM systems catch malicious traffic that the technologies above cannot. While Network AV might detect malicious attachments it will not identify malicious links in emails or known fraudulent emails.
Anti-SPAM works with email in a similar way to Network AV, rebuilding the original data and scanning it rather than inspecting packets. Member organisations can share logs relating to the potentially malicious emails with Police CyberAlarm, where the logs can be analysed and reported. The logs sent to Police CyberAlarm contain information about the source of the suspected spam, the email address of the intended recipient, the subject line and attachment name but not the body of the email. Anti-SPAM logs will reflect emails which have been blocked before reaching the end user, and will therefore not include information about emails which reach the end user but are diverted to a ‘Junk’ folder. Signing up to provide information about these logs gives Police CyberAlarm the ability to collect information on attempted attacks which could be targeting your organisation via email
Police CyberAlarm Vulnerability Scanning can be used to scan an organisation’s website and external IP addresses for known vulnerabilities. These regular reports can help increase an organisation’s cyber security, helping protect from known suspicious activity. Monthly vulnerability scanning helps to keep your network safe by identifying new threats that your external IPs and website URLs may face.
Member organisations can add regular vulnerability scanning of their website and external IP addresses. In order to scan for vulnerabilities the Police CyberAlarm system will scan your URLs and IP addresses to identify which services they allow requests to, for example if the system is a web server then it will allow web requests. The scanner software next attempts to identify the software and version on your system that is providing the service and compares these to international databases of registered security vulnerabilities and, where possible, tests to check if your organisation is vulnerable.
Every registered security vulnerability has a unique Common Vulnerability Exposures (CVE) code which can be used to look up the systems and versions affected by the vulnerability, its severity, as well as information on how best to mitigate and remediate the vulnerability.
Police CyberAlarm scans periodically to provide reports on new vulnerabilities that have been discovered for your organisation’s systems and, where possible, provides information from the CVE data to help your team remediate the vulnerability.
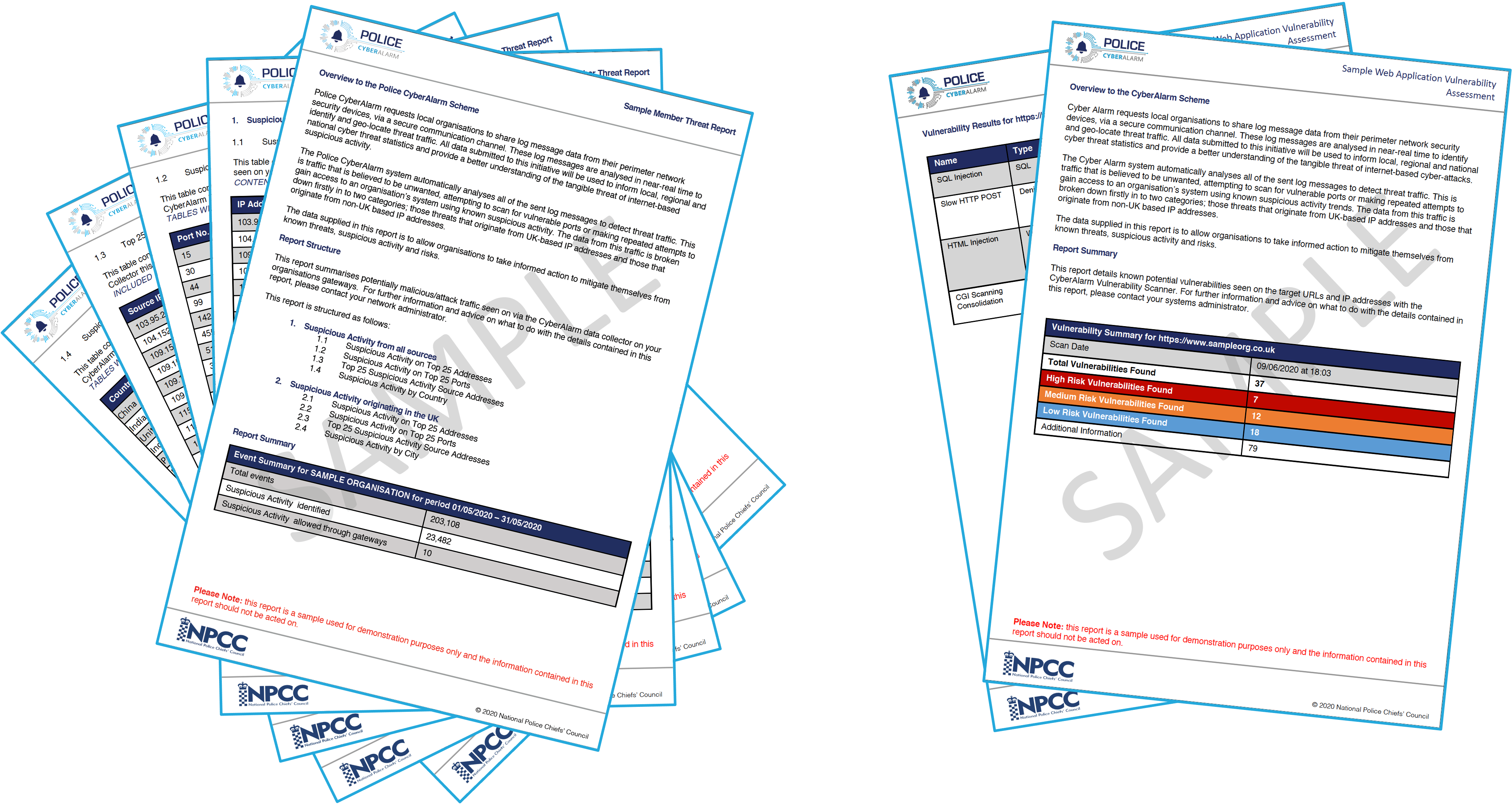
Members benefit from regular intelligence reporting, through their ‘Member Summary Threat Report’, summarising suspicious activity detected in the external traffic logs sent to their Police CyberAlarm collector. In addition to this report, members who opt in for vulnerability scanning will also receive a ‘Vulnerability Assessment Report’. This report details any potential vulnerabilities and the CVE codes for those vulnerabilities to help better protect the organisation.
This website stores data such as cookies to enable site functionality, more details can be found in our Privacy Policy and our Cookie Policy. By using this website, you agree to allow us to handle your data as set out in these policies.